Cipher & codes
1)Substitution Methods 2)Vigenere Cipher 3)Playfair Types 4)Bifid & Trifid methods 5)Columnar Transposition 6)Codes 7)Rail Fence Cipher 8)Some Other Used Ways 1)Substitution of letters by: a)Symbols: each letter is substituted with a letter or symbol or number. Letter: a b c d e f g h i j k l m n o p q r s t u v w x y z Subs.: 8 % j ) k 4 + $ g 5 d 9 ! d # r 2 i = f 7 * h 6 @ c MSG: I will return tomorrow. Subs: g hg99 ikf7id f#!#ii#h (easy isn't it??) so when your friend got the message , he(she) rewrite it with the substitution. b)Julius Caesar sub.: each letter is substituted with the letter next to it or few letters later. Letter: a b c d e f g h i j k l m n o p q r s t u v w x y z Subs.: D E F G H I J K L M N O P Q R S T U V W X Y Z A B C MSG: the mission is done Subs: WKH PLVVLRQ LV GRQH but for the security we group letters in units of 5 or more units because known letters like e & words like is, are, the,... make it easier to break the cipher so let?s see the last example: Subs: WKHPL VVLRQ LVGRQ H the last unit isn't full , you can insert any letters for better security Subs: WKHPL VVLRQ LVGRQ HSJBR so when your friend got the message ,he rewrites it in the original form and read every meaningful word regardless the spaces present using reversed form of the cipher substitution(decipher) Letter: A B C D E F G H I J K L M N O P Q R S T U V W X Y Z Subs.: x y z a b c d e f g h i j k l m n o p q r s t u v w MSG: themi ssion isdon epgyo (you see pgyo is meaningless) the mission is done Another forms: i)Julius Caesar with a keyword: here you start the subs. letters with a known word between you and your friend Let?s choose keyword (JULIUSCAESAR) first : we remove the repeated letters so it will be (JULISCAER) second : start the subs. letters with the keyword third : complete the substitution with the rest of letters in order which is not present in the keyword(lets see) Letter:a b c d e f g h i j k l m n o p q r s t u v w x y z Subs.: J U L I S C A E R B D F G H K M N O P Q T V W X Y Z here we observe that the last letters really match each other so we reverse the last matched letters with taking 1 or 2 previous letters. Letter:a b c d e f g h i j k l m n o p q r s t u v w x y z Subs.:J U L I S C A E R B D F G H K M N O P Q Z Y X W V T ii)Equivalent letters substitution: 2 letters are equivalent to each other. A B C D E F G H I J K L M EXAMPLE: how are you Z Y X W V U T S R Q P O N SLD ZIV BLF or A B C D E F G H I J K L M N O P Q R S T U V W X Y Z or A B C D E L M N F S T U V K J I H G R Q P O Z Y X W you can use any combination as you agreed with your friend. Break substituted message: The principle is that knowing the most frequent letters used in the language & substitute the frequent used letters in the message with it and try to find a known word then substitute with other letter has the same frequency. 1)The most frequent letters in English : E then T then A then O then N almost equals I then S then H,R,D,L(may slightly differ from text to other),rare letters may represent X or J or Q or Z 2)you get the most frequent letters in message: say W ,G,H equal number as K,C 3)you can get E & T substitution mostly but the next frequent letters you have to try & guess till you find good meaningful words, its like Scrabble somehow.(so W may represent E & G may represent T) Note: so even if you substitute the letters with graphs, only you and your friend know can be broken as it is a matter of statistics & try &some guess . 2)Vigenere cipher: Here you have large no.s of substitutions for every letter but if anyone has this table can use it also to decipher your message so you can randomize each alphabet in every row & you keep copy & your friend keep typical copy of it so you can use it safely. Example: M could be AM or OY or HF or ........................
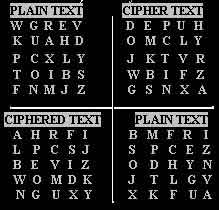
3)Playfair types: a)Simple playfair: it consists of 5 by 5 table and i) removing one letter may be QU represented as KW or ii) 1 letter represent 2 letters as U&V,I&J, we use U or V to represent both U&V so the 25 cell table can represent the alphabet 1 2 3 4 5 1 W G R E V 2 K U A H D 3 P C X L Y Here we substitute every 2 letters with other 2 from the table as follow 4 T O I B S 5 F N M J Z There are three cases: 1]The 2 letters aren't in the same row or column, we substitute as example: W--------------> E V How:1)make triangle with your eye between the 2 letters | U A | D 2)subs. every letter with the letter at the corner of the | C X | Y triangle at the moving clockwise to it. T < ------------- B S Examples: WB becomes ET F N M J Z UX becomes AC EF becomes JW 2]The 2 letters at the same row: W G R E V How:1)each letter becomes as the next letter to the right. K-->U A H-->D Examples: KH becomes UD P C X L Y WG becomes GR --->T O-->I B S--- NJ becomes MZ F N M J Z 2)if the letter is at the end of the row, you recycle to the first letter of the same row Examples: OS becomes IT RV becomes EW 3] The 2 letters at the same column: W G R E V How: 1) each letter becomes as the letter under it K U A H D Examples: UO becomes CN P C X L Y VS becomes DZ T O I B S 2) if the letter is at the end of the column, you recycle to F N M J Z the first letter of the same column Examples: RM becomes AR PF becomes TW 4] Special case :if you want to use the same letter twice: How: the letter becomes the letter under & to the right of the letter Example: UU becomes XX OO becomes MM or insert a pre-agreed letter between the 2 same letters so each of the same letter becomes with other letter & processed as usual. b)4 square playfair: i)has improved security as the letter is redirected to another square. ii)solve the problem of using double same letters. iii)here only the first rule is applied as we take letters from different squares.
 Notes:1)you may use a keyword as
previously used ,complete with
the rest of the alphabet, so you may
have up to 4 keywords!!
2) you can use only 2 squares, beside
each others in the same way, lets
work on the 2 upper squares:
Example: GF becomes UO, we use G from the
1st square and F from the 2nd
and subs. as the first rule in simple Playfair.
Notes:1)you may use a keyword as
previously used ,complete with
the rest of the alphabet, so you may
have up to 4 keywords!!
2) you can use only 2 squares, beside
each others in the same way, lets
work on the 2 upper squares:
Example: GF becomes UO, we use G from the
1st square and F from the 2nd
and subs. as the first rule in simple Playfair.
Examples:
UC becomes CP
RB becomes DR
BR becomes FF
4)Bifid , trifid cipher: It is somehow safe cipher as it causes the fractionation of every letter to 2 or more fractions. i)Bifid: Each letter is represented by 2 digits determine its location in the square. 1 2 3 4 5 How: you start from the left column numbers then go to the letter then to its 1 W G R E V upper number. 2 K U A H D Examples: G 1 2 3 P C X L Y A 2 3 4 T O I B S I 4 3 5 F N M J Z Message: THE TARGET IS UNDER FULL CONTROL 1) THETA RGETI SUNDE RFULL CONTR OL (each letter is represented by 2no.s 1st in the 1st row 2) 42142 11144 42521 15233 34541 43 ,2nd in the 2nd row just under the 1st) 14413 32413 52254 31244 22213 24 Note[ T = 4 1 , H = 2 4 , E = 1 4 , T = 4 1 , ..........] 3)take each 2 horizontal no.s and write their corresponding letter: 42 = O , 14 = E , 21 = K , 44 = B , 13 = R..........and so on 4214214413 1114432413 4252152254 1523331244 3454122213 4324 Ciphered: O E K B R W E I H R O N V U J V A X G B L J G U R I H ii)Trifid: each letter is represented by 3 digits(each range from 1 to 3) Q 111 B 121 X 131 S 211 K 221 U 231 D 311 Z 321 H 331 Y 112 M 122 I 132 A 212 V 222 J 232 O 312 G 322 P 332 F 113 R 123 W 133 L 213 E 223 ? 233 T 313 C 323 N 333 Notes:1)"?"can be any symbol as you want. 2)In any cipher you make random letter number association that only you and your friend knows it. Message: HELP WE LOST THE TARGET (by the same way as bifid) HELPW ELOST THETA RGET 32231 22323 33232 1323 32133 21111 13211 2221 13323 33213 31332 3233 322 313 213 313 323 223 232 111 133 213 332 321 321 131 332 132 322 312 233 Ciphered: G T L T C E J Q W L P Z Z X P I G O ? 5)Columnar transposition: 1)you make a keyword 2)numerate the letters from the nearest letter from the start of alphabet to the end & if you find repeated letters ,the first take the least number. Let?s see: we take espionage as our keyword: Message: THE MISSION IS OVER STOP ACTIVITY e s p o i n a g e 2 9 8 7 5 6 1 4 3 ---------------------------------------- WE GET: SRV TNOY OTT ISI IVT SEI MOC ESA HIP T H E M I S S I O N I S O V E R S T O P A C T I V I T Y To increase the security you can follow this: i)Double transposition: e s p o i n a g e e s p o i n a g e 2 9 8 7 5 6 1 4 3 2 9 8 7 5 6 1 4 3 ---------------------------------------- ---------------------------------------- T H E M I S S I O S R V T N O Y O T N I S O V E R S T T I S I I V T S E O P A C T I V I T I M O C E S A H I Y P WE GET: YTA STIP TEI OSH NIE OVS TIC VSO RIM ii)Different length transposition: e s p o i n a g e 2 9 8 7 5 6 1 4 3 Note: you write the letters of the message till ---------------------------------------- reach the numbers from 1 till the message T H E M I S S ends (we wrote THEMISS till we reached 1 I & I reached 2,...) O N I S O V E R S T O P A C T I V I T Y WE GET: SEI TIOTI S RV IOC SVT MSA EIPY HNOT iii)Leaving certain places never used in the square(only your friend know it) 6)Codes: i)Here we can increase the security of any cipher by giving code for certain word or expression or names & the better that every word got more than one code to express it(even you break the cipher you don't know what it is talking about!) ii)This codes are saved by the spy in a book, always it is very small(can be hidden inside a concealment coin!!) to ease its concealment & the codes are well organized alphabetically for rapid coding & decoding. Example: i)Neutral codes: plaintext code group cab YABC cabal YBCD cabin YCDE cable YDEF cache YEFG ii)One-sided codes: plaintext code group cab JGRD cabal BCFD cabin LVDH cable MFHY cache NFES decode code group plaintext APGR London APND minister APTD however APMC 100 km APVD money 7)Railfence cipher: here you write the words in certain ways to be readable Example: 1 r n 2 a e c 3 i f e 4 l so the ciphered will appear like rnaec ifel you can use any shape you want in definite rows W or N or S anything. 8)Some other used ways: i)Newspaper & a pin: this is an old way to leave a message, the spy sit reading some newspaper and forget it on the seat(very smart, anyone can point this is not a spy?!),then other innocent guy come & sit at the same seat, wow, really comfortable seat, then he by accident find a newspaper , his favorite one, nice, here start the trick, he search for a tiny pin orifice appear infront of light under certain letters of the newspaper, following this holes form words and message. Note: it also used in dictionaries as you know where is the message but any other guy must search the whole dictionary in front of light. ii)Books: 1)you must get 2 identical books, the same edition ,identical from cover to cover, every word. 2)you want to make a secret message to your friend, you take your book, find a cool page ,write its number in the start of the message, you may cipher it or apply a mathematical equation to ensure that even someone got the message & try it to the books you have, can't extract it. 3)start from the first line of this page or certain line (you & your friend agreed to it), you write the number which represent your first letter in the first letter, then go to the next line and write the number which represent your second letter, you count the spaces also, comma's, every thing. 4)If you get to line where you didn't find the letter you want ,you write certain letter (you both know), so your friend skips this line & proceed to the next one , it is very secure and really simple. Note: The presence of an original script of a ciphered messages or codes is of great importance to the code breakers in cryptanalysis, so they have to reform the message in other words ,for this reason that the secret services always try to steal the cipher and code books. Links Cipher Clerk nice site java applet makes different ciphers types and deciphering , you can use it to cipher and decipher messages with your friends just with copy and paste. PGP encrypt & secure your mails , secure your business communications.
TO THE TOP
|
Quote"" Dream what you want to dream, go where you want to go, & be what you want to be, because you have only one life and one chance to do all the things you want"" |
[ Home | SpyingWorld | CounterIntelligenceMen | Ciphers&Codes | InvisibleInks | SpiesCities |
|
The site design is made by Mohammed S. Anwar. All the compiled informations & links are personal effort and
gathered from different resources on the internet and from books, it is not my own creativity, but i just compiled what I thought that it is interesting ,in my own writing style . All the copyrights are reserved to the original authors.
You are free to copy ,print, distribute any part of the site , in case you don't take any money or change any parts of it. |